Do you know what amazing thing the Unified Threat Intelligence Platform (UTIP) is? If not, then you really need to know about it. Here, we will talk about how this platform works and offer you chances to be prepared for cyber threats.
Moreover, we will introduce you to a reliable platform that can offer you similar services for better protection against unknown online threats. What are we waiting for? Let’s get started!
The Growing Cyber Threat Landscape
A growing arms race characterizes the global cyber threat scene in 2026, and AI-driven automation has significantly shortened the time between first reconnaissance and effective exploitation.
In order to get beyond traditional security perimeters, adversaries are moving from classic malware-based incursions to identity-centric attacks, increasingly using deepfakes, autonomous AI agents, and supply chain vulnerabilities.
Organizations are facing a growing "confidence gap," finding it difficult to keep up with the speed and flexibility of attackers who are now taking advantage of interconnected systems more quickly than ever before, as these complex, hyper-personalized campaigns become the new norm.
What Is a Unified Threat Intelligence Platform?
As a centralized, data-driven command center, a Unified Threat Intelligence Platform (UTIP) compiles, standardizes, and correlates various security signals from throughout a whole digital infrastructure.
Security teams may more accurately identify, prioritize, and neutralize sophisticated attacks thanks to the integration of external threat feeds with internal telemetry, which turns fragmented raw data into actionable insights.
This all-encompassing strategy greatly reduces alert fatigue and speeds up incident reaction times by substituting automated, risk-based decision-making for manual analysis.
Why “Unified” Matters in Modern Cybersecurity?
Unified matters in modern cybersecurity for the following reasons:
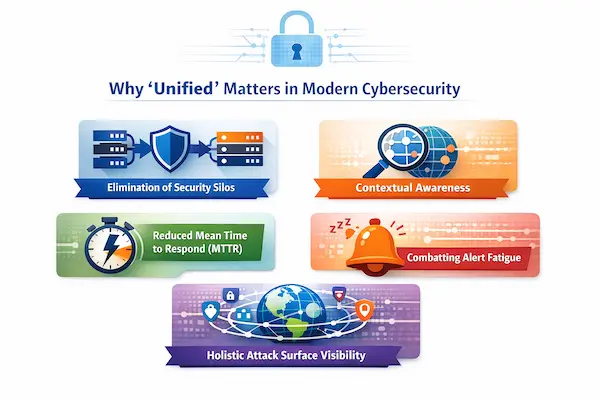
1. Elimination of Security Silos: Ensures that no threat is overlooked by centralizing disparate data into a single source of truth.
2. Contextual Awareness: Gives each security occurrence a deeper significance by correlating internal and external intelligence.
3. Reduced Mean Time to Respond (MTTR): Simplifies processes to allow for quick, automated responses to risks that have been recognized.
4. Combatting Alert Fatigue: Eliminates noise by giving high-fidelity alerts priority, allowing teams to concentrate solely on serious threats.
5. Holistic Attack Surface Visibility: Gives a comprehensive, up-to-date map of all the organization's assets and exposures.
How a Unified Threat Intelligence Platform Works?
|
S.No. |
Factors |
How? |
|
1. |
Data Collections |
Automatically absorbs enormous amounts of telemetry from external global threat feeds, cloud environments, and internal logs. |
|
2. |
Data Normalization |
Ensures that all security products can interact with one another by converting various data formats into a common framework. |
|
3. |
Enrichment & Correlation |
Cross-referencing raw data with known attacker patterns and prior breach archives adds crucial context. |
|
4. |
Threat Scoring & Prioritization |
Highlights the most serious risks by giving each event a risk level based on its possible impact and severity. |
|
5. |
Automated Response |
Seamlessly integrates with security orchestrators to initiate quick protective measures, such as banning IPs or isolating hosts. |
Types of Threat Intelligence
The following are the types of threat intelligence:
● Strategic Intelligence: Principally aims to support executive-level decision-making and enterprise security posture by offering high-level insights on more general threat trends and risk landscapes.
● Tactical Intelligence: Explains the precise Tactics, Techniques, and Procedures (TTPs) that adversaries employ, assisting security teams in setting up defenses to prevent typical attack pathways.
● Operational Intelligence: Enables proactive planning and incident management by providing real-time information on particular, upcoming, or current assaults against an organization.
● Technical Intelligence: Consists of specific, machine-readable Indicators of Compromise (IoCs) that are utilized for automated blocking, such as malicious IP addresses, file hashes, and domain names.
Key Features of a Unified Threat Intelligence Platform
The following are the key features of a UTIP:
a) Agentic AI & Multi-Agent Systems: Install autonomous AI bots that can look for threats, analyze alarms, and organize defenses on their own without continual human supervision.
b) External Attack Surface Management (EASM): Finds and keeps an eye on every asset that is connected to the internet in order to spot weaknesses and observe IT from the viewpoint of an attacker.
c) Predictive Threat Forecasting: Makes use of cutting-edge machine learning to examine worldwide trends and forecast the most likely targets and attack strategies before they happen.
d) Automated Data Orchestration: Ensures real-time coordination and response by seamlessly coordinating the flow of intelligence across several security systems.
e) Deep Dark Web Intelligence: Keeps an eye on underground forums and marketplaces to spot stolen data from your company, planned campaigns, or compromised passwords.
Benefits of Using a Unified Threat Intelligence Platform
|
S.No. |
Benefits |
How? |
|
1. |
Proactive Threat Detection |
Integrates worldwide intelligence to find and stop new threats before they have a chance to affect your internal systems. |
|
2. |
Faster Incident Response |
Streamlines workflows across all security products and automatically aggregates context to speed up investigation and response. |
|
3. |
Reduced Alert Fatigue |
Ensures that security analysts only concentrate on high-fidelity, actionable threats by filtering out noise and noise-prone false positives. |
|
4. |
Better Decision Making |
Gives leadership high-level, data-driven insights that match security spending to real risk exposure and corporate priorities. |
Use Cases of Unified Threat Intelligence Platforms
The following are some of the use cases of UTIP:
1. Automated Incident Response: Firewalls and EDR systems can instantly block malicious IPs or isolate infected endpoints as soon as a threat is detected by directly integrating real-time threat intelligence.
2. Proactive Vulnerability Prioritization: Patching the most "weaponized" vulnerabilities rather than just the highest-scoring ones by cross-referencing internal asset inventories with external exploit databases and dark web discussions.
3. Advanced Third-Party Risk Management: Keeping a close eye on partners' and vendors' digital footprints and dark web presence to spot possible supply chain hazards before they become an organizational breach.
Why Businesses Need It in 2026 and Beyond?
Businesses need it in 2026 and beyond for the following reasons:
● Countering AI-Driven Speed: Defenses against dangers that now spread and change at machine speed, considerably faster than human reaction times, by automating defense mechanisms.
● Closing Visibility Gaps: Ensures that no entry point or vulnerability is hidden by dismantling data silos to present a thorough picture of the threat landscape.
● Managing Escalating Complexity: Unifies several tools and telemetry into a single, coherent intelligence framework, simplifying the security stack.
● Shifting to Continuous Exposure Management: Goes beyond sporadic point-in-time evaluations to a continuous state of observation and flexible protection against changing threats.
● Aligning Security with Business Risk: Converts intricate technical data into useful insights that directly assist in resource allocation and corporate decision-making.
How ThreatFusionAI Fits Into This Ecosystem?
|
S.No. |
Factors |
How? |
|
1. |
Comprehensive Threat Database |
It has a sizable database on people and businesses affected by phishing and data breaches, which is essential historical information for threat hunting. |
|
2. |
AI-Powered Detection |
In order to identify complex, polymorphic phishing attempts and other malicious behaviors that evade conventional signature-based filters, the platform uses artificial intelligence to evaluate patterns. |
|
3. |
Intelligence Correlation |
By correlating raw threat data, it bridges the gap between diverse security signals and enables security teams to convert fragmented logs into high-fidelity, actionable insight. |
|
4. |
Operational Integration |
It is an essential part of the "House of Craw Security" ecosystem and collaborates with programs like ShieldXDR to offer a smooth feedback loop between automated defense and threat detection. |
|
5. |
Adaptive Defense Posture |
Ensuring that defensive measures are continuously updated based on real-time knowledge about changing opponent tactics, it enables enterprises to transition from reactive firefighting to a proactive position. |
How to Choose the Right Unified Threat Intelligence Platform?
In the following ways, you can choose the right unified threat intelligence platform:

a) Seamless Integration Capabilities: To guarantee a unified, automated security stack, give top priority to platforms that provide reliable, pre-built interfaces for your current SIEM, SOAR, EDR, and cloud infrastructure.
b) Actionable Context & Transparency: To help analysts comprehend the "why" behind each alert, look for solutions that offer unambiguous, richer intelligence, such as actor attribution and confidence score.
c) Scalability & Performance: Select an architecture that can collect, normalize, and analyze enormous amounts of heterogeneous data in real-time without adding latency to your security operations.
d) Intuitive User Experience: Choose a platform that lowers the entry barrier for both beginner and experienced analysts by having an easy-to-use interface and visual investigative tools like link analysis.
e) Alignment with Business Risk: Make sure the platform allows you to prioritize risks that are most important to your company by mapping technological threats to your unique business assets and regulatory requirements.
Future of Threat Intelligence Platforms
In 2026 and beyond, autonomous, predictive engines that use agentic AI to foresee and destroy threats before they arise will replace reactive data aggregation in threat intelligence platforms. In order to effectively break down silos and provide real-time, risk-aligned insights that enable security teams to react to machine-speed threats with automated precision, these platforms will increasingly concentrate on identity-centric intelligence and continuous exposure management.
Conclusion
Now that we have talked about Unified Threat Intelligence Platform, you might want to get a reliable platform for that. For that, you can get in contact with Craw Security, offering Threat Fusion AI, a dedicated threat detection platform for organizations running in the IT Industry.
This platform will tell you beforehand what kind of threat is going to risk your security, and you will be able to prepare for it in advance by enhancing your security measures. What are you waiting for? Contact, Now!
Frequently Asked Questions (FAQs)
About Unified Threat Intelligence Platform
1. What is a Unified Threat Intelligence Platform?
A Unified Threat Intelligence Platform is a unified security solution that turns fragmented threat information into actionable, risk-prioritized insights by aggregating, normalizing, and correlating data from various internal and external sources.
2. How is a Unified Threat Intelligence Platform different from a traditional TIP?
In contrast to a traditional TIP, which mainly serves as a passive, compartmentalized repository for collecting and managing external threat feeds, a Unified Threat Intelligence Platform integrates threat data directly with internal telemetry and automated security orchestration to provide actionable, business-aligned responses.
3. Why is threat intelligence important for organizations?
For the following reasons, threat intelligence is important for organizations:
a) Informed Decision-Making,
b) Faster Detection & Response,
c) Proactive Vulnerability Management,
d) Reduced Operational Friction, and
e) Strategic Advantage Against Sophisticated Adversaries.
4. What types of data does a Unified Threat Intelligence Platform collect?
UTIP collects the following types of data:
a) Internal Security Telemetry,
b) External Threat Feeds,
c) Dark Web and Underground Intelligence,
d) Adversary Tactics, Techniques, and Procedures (TTPs), and
e) Vulnerability and Asset Data.
5. Can small and medium-sized businesses benefit from a Unified Threat Intelligence Platform?
Yes, these solutions provide enterprise-grade, automated threat defense and proactive risk prioritization, which help small and medium-sized enterprises overcome their sometimes insufficient cybersecurity manpower and resource shortages.
6. How does a Unified Threat Intelligence Platform reduce alert fatigue?
In the following ways, a UTIP reduces alert fatigue:
a) Contextual Alert Enrichment,
b) Deduplication and Noise Reduction,
c) Automated Triage and Prioritization,
d) Suppression of Known False Positives, and
e) Integration with Automated Response (SOAR).
7. Does a Unified Threat Intelligence Platform integrate with existing security tools?
Yes, by utilizing reliable APIs and pre-built connectors to synchronize telemetry and coordinate automated, cross-platform responses, a Unified Threat Intelligence Platform easily integrates with current security solutions like SIEM, SOAR, EDR, and firewalls.
8. What role does AI play in threat intelligence platforms?
AI plays the following roles in threat intelligence platforms:
a) Autonomous Threat Detection and Hunting,
b) Predictive Threat Forecasting,
c) Contextual Enrichment and Storyline Generation,
d) Automated Incident Triage and Response, and
e) Continuous Adaptive Learning.
9. How does a Unified Threat Intelligence Platform improve incident response time?
In the following ways, UTIP improves incident response time:
a) Automated Data Enrichment,
b) Centralized Incident View,
c) Orchestrated Response Workflows,
d) Prioritized Remediation Guidance, and
e) Collaboration and Communication Sync.
10. Is a Unified Threat Intelligence Platform necessary in 2026 and beyond?
A Unified Threat Intelligence Platform is not just critical but fundamental in 2026 because it offers the automated, real-time intelligence needed to counter machine-speed, AI-driven cyber threats that have left fragmented, manual security operations outdated.